Jnk (Diskussion | Beiträge) K (Internet Link auf "Formatierung offizieller ZIM E-Mails geändert") |
|||
| (8 dazwischenliegende Versionen von 2 Benutzern werden nicht angezeigt) | |||
| Zeile 12: | Zeile 12: | ||
This may well include targeted attacks, which may be embedded in conversation histories. Therefore, you should use the checklist below for every e-mail. With a little routine, just a few seconds are enough to prevent immense damage. | This may well include targeted attacks, which may be embedded in conversation histories. Therefore, you should use the checklist below for every e-mail. With a little routine, just a few seconds are enough to prevent immense damage. | ||
| − | {{Mbox|text=The | + | {{Mbox|text=The ZIM staff will '''NEVER''' ask you for your password. Do ''not'' answer questions about this over the phone or email!}} |
---- | ---- | ||
| Zeile 19: | Zeile 19: | ||
The answer is essentially always, yes. It is much easier for an attacker to gain access to systems via phishing than via attacks based purely on a technical attack vector. Even if you do not have access to important infrastructure credentials, significant damage can still be done with your login data. Simply having access to your email inbox can help an attacker inspire more trustworthiness, as they now have access to conversation histories and may also be able to use your email address. | The answer is essentially always, yes. It is much easier for an attacker to gain access to systems via phishing than via attacks based purely on a technical attack vector. Even if you do not have access to important infrastructure credentials, significant damage can still be done with your login data. Simply having access to your email inbox can help an attacker inspire more trustworthiness, as they now have access to conversation histories and may also be able to use your email address. | ||
| − | Phishing is a significant threat. | + | Phishing is a significant threat. Simply by double checking or not rashly opening a link or file you don't recognize, you can prevent significant damage. |
---- | ---- | ||
| Zeile 35: | Zeile 35: | ||
*If you know who oversees your infrastructure, contact that person (preferably by phone) | *If you know who oversees your infrastructure, contact that person (preferably by phone) | ||
*[https://www.uni-paderborn.de/en/university/universitaet/informationssicherheit/reporting-of-information-security-incidents/ Report the incident] to [mailto:vorfall@upb.de vorfall@upb.de] | *[https://www.uni-paderborn.de/en/university/universitaet/informationssicherheit/reporting-of-information-security-incidents/ Report the incident] to [mailto:vorfall@upb.de vorfall@upb.de] | ||
| − | *If you are unsure, contact the [https://imt.uni-paderborn.de/en/hotline-phone-e-mail | + | *If you are unsure, contact the [https://imt.uni-paderborn.de/en/hotline-phone-e-mail ZIM Hotline] at (05251) 60-5544 or at [mailto:zim@uni-paderborn.de zim@uni-paderborn.de] |
---- | ---- | ||
| Zeile 53: | Zeile 53: | ||
#*Does the email signal a need for action or urgency? | #*Does the email signal a need for action or urgency? | ||
#*Are there any abnormalities in the formatting? | #*Are there any abnormalities in the formatting? | ||
| − | #**Do | + | #**Do ZIM emails follow the [[Formatierung offizieller ZIM E-Mails]]? |
#*Is the salutation impersonal? | #*Is the salutation impersonal? | ||
#*Does the email ask for passwords or personal information? | #*Does the email ask for passwords or personal information? | ||
| Zeile 83: | Zeile 83: | ||
Where a link leads to is not always obvious. Therefore, here are some examples to make it easier to recognize the actual destination of a link and identify the actual sender. | Where a link leads to is not always obvious. Therefore, here are some examples to make it easier to recognize the actual destination of a link and identify the actual sender. | ||
| − | + | None of the characters in the domain can be changed by an attacker. This means that you can only tell if a link is trustworthy by looking at the domain. | |
The section of the e-mail address that is not part of the domain is often exploited to give the appearance of trustworthiness, as even the text uni-paderborn.de, for example, can be used in these areas by an attacker. | The section of the e-mail address that is not part of the domain is often exploited to give the appearance of trustworthiness, as even the text uni-paderborn.de, for example, can be used in these areas by an attacker. | ||
| Zeile 110: | Zeile 110: | ||
*<span style="color: gray;">mustername.musternachname@uni-paderborn.</span><span style="color: red;">unimail.de</span> | *<span style="color: gray;">mustername.musternachname@uni-paderborn.</span><span style="color: red;">unimail.de</span> | ||
*<span style="color: gray;">uni-paderborn@</span><span style="color: red;">mustername.de</span> | *<span style="color: gray;">uni-paderborn@</span><span style="color: red;">mustername.de</span> | ||
| − | |||
== Reviewing the Changelog of your university account == | == Reviewing the Changelog of your university account == | ||
In the Changelog you can check whether the statement of a warning mail about the suspension of your account is true. | In the Changelog you can check whether the statement of a warning mail about the suspension of your account is true. | ||
<br clear=all> | <br clear=all> | ||
| − | [[Datei: | + | [[Datei:Screenshot_SP_Menu.png|links|mini|ohne|605x605px]] |
<br> | <br> | ||
| − | * Open the | + | * Open the ZIM service portal: https://sp.uni-paderborn.de |
* Log in with your university account data. | * Log in with your university account data. | ||
| − | * In the menu "User administration" select the item '''"Uni account''' (The access created after successful enrollment (students) or employment (employees) at the | + | * In the menu "User administration" select the item '''"Uni account''' (The access created after successful enrollment (students) or employment (employees) at the ZIM.) '''settings"'''. |
<br clear=all> | <br clear=all> | ||
| − | [[Datei: | + | [[Datei:Screenshot_Show_Changelog.png|links|mini|ohne|605x605px]] |
<br> | <br> | ||
| − | * Then select the "''' | + | * Then select the "'''Show Changelog'''" item and check the log for suspension processes. |
<br clear=all> | <br clear=all> | ||
| Zeile 171: | Zeile 170: | ||
# Sender | # Sender | ||
#* Domain of the sender address is correct | #* Domain of the sender address is correct | ||
| − | #* Such e-mails from the | + | #* Such e-mails from the ZIM usually come from zim@uni-paderborn.de |
# Content | # Content | ||
#* Unexpected e-mail | #* Unexpected e-mail | ||
| Zeile 256: | Zeile 255: | ||
# Sender | # Sender | ||
#* Domain of the sender address is correct | #* Domain of the sender address is correct | ||
| − | #* Such e-mails from the | + | #* Such e-mails from the ZIM usually come from zim@uni-paderborn.de |
# Content | # Content | ||
#* Unexpected e-mail | #* Unexpected e-mail | ||
| Zeile 276: | Zeile 275: | ||
== Further information == | == Further information == | ||
* [[Informationssicherheit | Information security]] - Overview of all articles | * [[Informationssicherheit | Information security]] - Overview of all articles | ||
| − | * [[Formatierung offizieller | + | * [[Formatierung offizieller ZIM E-Mails | Formatting of official ZIM mails]] - This is how official mails from the ZIM are labeled |
* [[Aenderung des Kennwortes | Changing the password]] - The quick precaution in case of suspicion: changing your own password | * [[Aenderung des Kennwortes | Changing the password]] - The quick precaution in case of suspicion: changing your own password | ||
<br clear=all> | <br clear=all> | ||
Aktuelle Version vom 26. Juni 2024, 14:58 Uhr
Unfortunately, e-mail addresses from the university namespace are repeatedly misused to send spam and phishing e-mails. Please be suspicious if you receive an email that you cannot assign to any context.
Phishing[Bearbeiten | Quelltext bearbeiten]
One method of attack to obtain usernames and passwords are so-called phishing e-mails. Phishing refers to attempts to obtain an Internet user's data via fake websites, e-mail or short messages and thus commit identity theft. The aim of the fraud is to use the data obtained, for example, to plunder the bank account and harm the relevant persons.
This may well include targeted attacks, which may be embedded in conversation histories. Therefore, you should use the checklist below for every e-mail. With a little routine, just a few seconds are enough to prevent immense damage.
The ZIM staff will NEVER ask you for your password. Do not answer questions about this over the phone or email! |
Am I a potential target?[Bearbeiten | Quelltext bearbeiten]
The answer is essentially always, yes. It is much easier for an attacker to gain access to systems via phishing than via attacks based purely on a technical attack vector. Even if you do not have access to important infrastructure credentials, significant damage can still be done with your login data. Simply having access to your email inbox can help an attacker inspire more trustworthiness, as they now have access to conversation histories and may also be able to use your email address.
Phishing is a significant threat. Simply by double checking or not rashly opening a link or file you don't recognize, you can prevent significant damage.
What to do if I have been deceived?[Bearbeiten | Quelltext bearbeiten]
| If you have revealed your university account login information in a phishing attack, please change your password immediately. You can find instructions on how to change your password in the article Changing the password. |
It is important to make a report as soon as you suspect that you have been deceived by a phishing message. The only way to limit possible damage is for our experts to respond to such a situation as quickly as possible. The faster, the better.
There are three ways to make such a report:
- If you know who oversees your infrastructure, contact that person (preferably by phone)
- Report the incident to vorfall@upb.de
- If you are unsure, contact the ZIM Hotline at (05251) 60-5544 or at zim@uni-paderborn.de
Checklist for distinguishing spam and phishing messages[Bearbeiten | Quelltext bearbeiten]
- Check the sender
- Is the email address really from the expected sender?
- info@uni-paderborn.de
- info@unl-paderborn.de
- Can you verify the email address?
- By comparing it with a known e-mail address
- By contacting the sender (by phone or via a verified email address)
- A legitimate sender alone is not a sign of a trustworthy email, as its email box may have been compromised by a possible attacker.
- Is the email address really from the expected sender?
- Check the content (Does the content seem suspicious to you?)
- Is the sender's message expected?
- Does the email signal a need for action or urgency?
- Are there any abnormalities in the formatting?
- Do ZIM emails follow the Formatierung offizieller ZIM E-Mails?
- Is the salutation impersonal?
- Does the email ask for passwords or personal information?
- Check the links (Are the displayed links trustworthy?)
- What destination URL is displayed in the status bar when you hover over the link?
- Does the domain match a trusted mail?
- serviceportal.uni-paderborn.de
- uni-paderborn.serviceportal.de
- Is the domain spelled correctly?
- serviceportal.uni-paderborn.de
- serviceportal.uni-padreborn.de
- Check the attachment
- Open files only if you consider them absolutely trustworthy
- Beware of file formats, such as .exe or .bat
- Invoice-18-05-2021.pdf
- Invoice-18-05-2021.pdf.exe
- Avoid activating macros in Microsoft Office documents at all costs
- In case of doubt (e.g., even if you have a "funny feeling") make sure to contact the sender via an alternative way, e.g., by phone.
| If even one of the above points arouses suspicion, contact the sender or delete the e-mail. If you are unsure, you can always consult a colleague. |
Domains[Bearbeiten | Quelltext bearbeiten]
Where a link leads to is not always obvious. Therefore, here are some examples to make it easier to recognize the actual destination of a link and identify the actual sender.
None of the characters in the domain can be changed by an attacker. This means that you can only tell if a link is trustworthy by looking at the domain.
The section of the e-mail address that is not part of the domain is often exploited to give the appearance of trustworthiness, as even the text uni-paderborn.de, for example, can be used in these areas by an attacker.
The most commonly used official domains of the University of Paderborn are upb.de and uni-paderborn.de.
Domain of a link[Bearbeiten | Quelltext bearbeiten]
The domain of a link is delimited by dots . and dashes /. Important are the characters before and after the last dot to the first dash. So, for the link https://serviceportal.uni-paderborn.de/web/portal/registrierung the domain is uni-paderborn.de.
- https://serviceportal.uni-paderborn.de
- https://uni-paderborn.serviceportal.de
- http://dokumente.de/uni-paderborn.de/
- http://131.234.152.9/upb.de/
Domain of an E-Mail address[Bearbeiten | Quelltext bearbeiten]
The domain of an email address is enclosed by dots and the at-sign @. Important are again the characters before and after the last dot. So, for the e-mail address mustername.musternachname@mail.uni-paderborn.de the domain is uni-paderborn.de.
- mustername.musternachname@uni-paderborn.de
- mustername.musternachname@uni-paderborn.unimail.de
- uni-paderborn@mustername.de
Reviewing the Changelog of your university account[Bearbeiten | Quelltext bearbeiten]
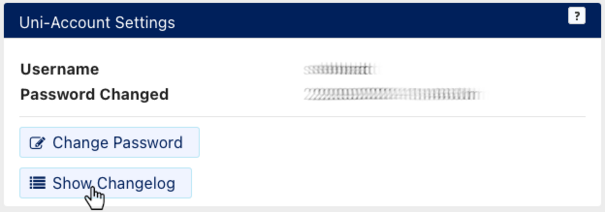
In the Changelog you can check whether the statement of a warning mail about the suspension of your account is true.
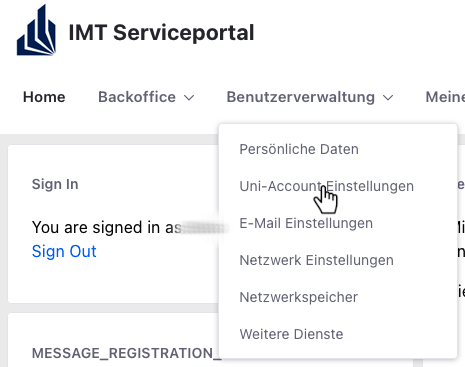
- Open the ZIM service portal: https://sp.uni-paderborn.de
- Log in with your university account data.
- In the menu "User administration" select the item "Uni account (The access created after successful enrollment (students) or employment (employees) at the ZIM.) settings".
- Then select the "Show Changelog" item and check the log for suspension processes.
FAQ and first aid in case of email phishing and other data leakage[Bearbeiten | Quelltext bearbeiten]
If you have been, or could be, a victim of a phishing attack, or sensitive data of yours has been exposed in some other way, you may face threats as a result. In such a case, many questions and emotions typically arise among those affected. The following overview is intended to provide some answers to possible questions and give advice on how to deal with them and the steps that need to be taken.
What consequences can the leakage of sensitive data have for me?[Bearbeiten | Quelltext bearbeiten]
It is conceivable that third parties could attempt to use stolen data for criminal purposes.
In case of outflow of contact information (e.g., e-mail address, phone number):[Bearbeiten | Quelltext bearbeiten]
The more information attackers have about a person, the easier it is for them to impersonate that person and "steal" their identity with malicious intent. This can lead to downstream phishing attacks, for example, in which attackers can fake a false sender and thus persuade other people (colleagues, business partners, etc.) to hand over sensitive data.
- Note: The university email addresses are (especially for employees) often already published via the university websites and thus publicly known.
In case of leakage of login data incl. passwords:[Bearbeiten | Quelltext bearbeiten]
- Third parties can log in to all services that use the leaked login information (university email, PAUL, PANDA, network storage, service portal, Personmanager, SharePoint, etc.)
- thereby third parties gain access to further sensitive data such as e-mails, files, grades, ...
- Furthermore, the manipulation of data, the loss of confidentiality of data, the violation of non-disclosure agreements (e.g., in research projects) as well as the theft of (research) data are possible as a result.
What should I do if my login data has been exposed (e.g., by phishing)?[Bearbeiten | Quelltext bearbeiten]
See: "What to do if I have been deceived?"
Examples of phishing messages[Bearbeiten | Quelltext bearbeiten]
Example_False_Note_on_Update
From: University of Paderborn [mailto:noreply@upb.de] Sent: Friday, October 23 2015 00:51 To: winner Subject: UPDATE!!! University of Paderborn has released new version web-mail, 2015 edition. This latest web-mail version comes with new and enhanced features secured and anti-spam protection. It is recommended, please click here today to migrate and enable the advanced security features. Sincerely, © 2015 Informatics Service.
- Sender
- Domain of the sender address is correct
- Such e-mails from the ZIM usually come from zim@uni-paderborn.de
- Content
- Unexpected e-mail
- Suggesting the need for action, urging you to act quickly and rashly
- Unusual formatting (email does not follow official formatting)
- Impersonal salutation
- Links
- The next step here would be to check the link provided (the true destination of the link will only be shown to you in the status bar of your email program).
Example_CustomerService
Date: Mon, Nov 10 2014 19:10:23 +0100
From: Telekom Head of Customer Service <werbung@mmgarten.com>
Subject: InvoiceOnline month November 2014 (posting account: 5405293552).
To: rza@mail.uni-paderborn.de
TELEKOM - EXPERIENCE WHAT CONNECTS.
Telekom Head of Customer Service
Your bill for November 2014
Good day,
With this e-mail you will receive your current
invoice. The total amount in the month of November 2014 is: 166,92 EURO.
In the attachment you will find the requested documents for your mobile
communications InvoiceOnline for November 2014. Your invoice for November 2014[1] - (PDF document).
This message was sent automatically. Please do not reply to the sender's address.
Yours sincerely
Ralf Hoßbach
Head of Customer Service
© Telekom Head of Customer Service 2014 | Help | Contact | Privacy | T&C | Imprint
Do you have a question for customer service? Then please use our e-mail contact form.
Links:
------
[1] http://hostomanXXXX.net/XXXXXX (modified)
- Sender
- The domain of the sender address is conspicuous for an e-mail that is supposed to come from Telekom.
- If unsure, contact Telekom using contact data you have researched yourself.
- Content
- Impersonal salutation
- Links
- The domain of the link (hostomanXXXX.net) does not match an e-mail from Telekom.
- Attachment
- With the conspicuous features described above, you should not open the attachment of this e-mail or only after very thorough consultation (via an alternative communication channel).
Example_False_Mail_Warning
From: University of Paderborn <noreply@upb.de> Subject: Urgent Notification!!! Date: May 12 2014 02:35:18 CEST To: Recipients <noreply@upb.de> Reply to: noreply@upb.de Dear User, You are receiving this message from webmailservice@upb.de. Your email account was hacked / compromised and used for various spam / phishing activities Please click or copy universal following link and change your account details, http:/upb.com/correo/account Please note that fail to do is resulting in the cancellation of your account. Webmail Team
- Sender
- Domain of the sender address is correct
- Such e-mails from the ZIM usually come from zim@uni-paderborn.de
- Content
- Unexpected e-mail
- Suggesting the need for action, urging you to act quickly and rashly
- Unusual formatting (email does not follow official formatting)
- Impersonal salutation
- Links
- The text in the email could have been chosen arbitrarily (here http:/upb.de/correo/account) only the link displayed in the status bar is the true target.
Can you recognize phishing emails?[Bearbeiten | Quelltext bearbeiten]
Test your IT security awareness via these products by KIT research group SECUSO (Security Usability and Society):
- What score can you achieve in the Phishing-Master game?
- https://phishing-master.secuso.org/ (Currently only available in German)
- Can you recognize all fraudulent emails in the NoPhish Quiz?
- https://nophish-quiz.secuso.org/ (Currently only available in German)
Further information[Bearbeiten | Quelltext bearbeiten]
- Information security - Overview of all articles
- Formatting of official ZIM mails - This is how official mails from the ZIM are labeled
- Changing the password - The quick precaution in case of suspicion: changing your own password